SYS.DOCS // DOCS
Domains and Wildcard TLS
Edka manages cluster level wildcard domains for deployments and previews. Standard hostnames can be configured for each deployment, but can not be assigned to a preview environment.
Domain types
- Wildcard domains:
*.example.comfor production or staging deployments. - Preview wildcard domains:
*.preview.example.commarked as preview for pull request previews.
Notes:
- Only wildcard domains are supported in the cluster Domains view.
- Wildcards are single level.
*.example.commatchesapp.example.com, notapp.dev.example.com. - Each domain is tied to an ingress class.
- Multiple preview wildcard domains per ingress class are supported. Each Git deployment can select a specific one.
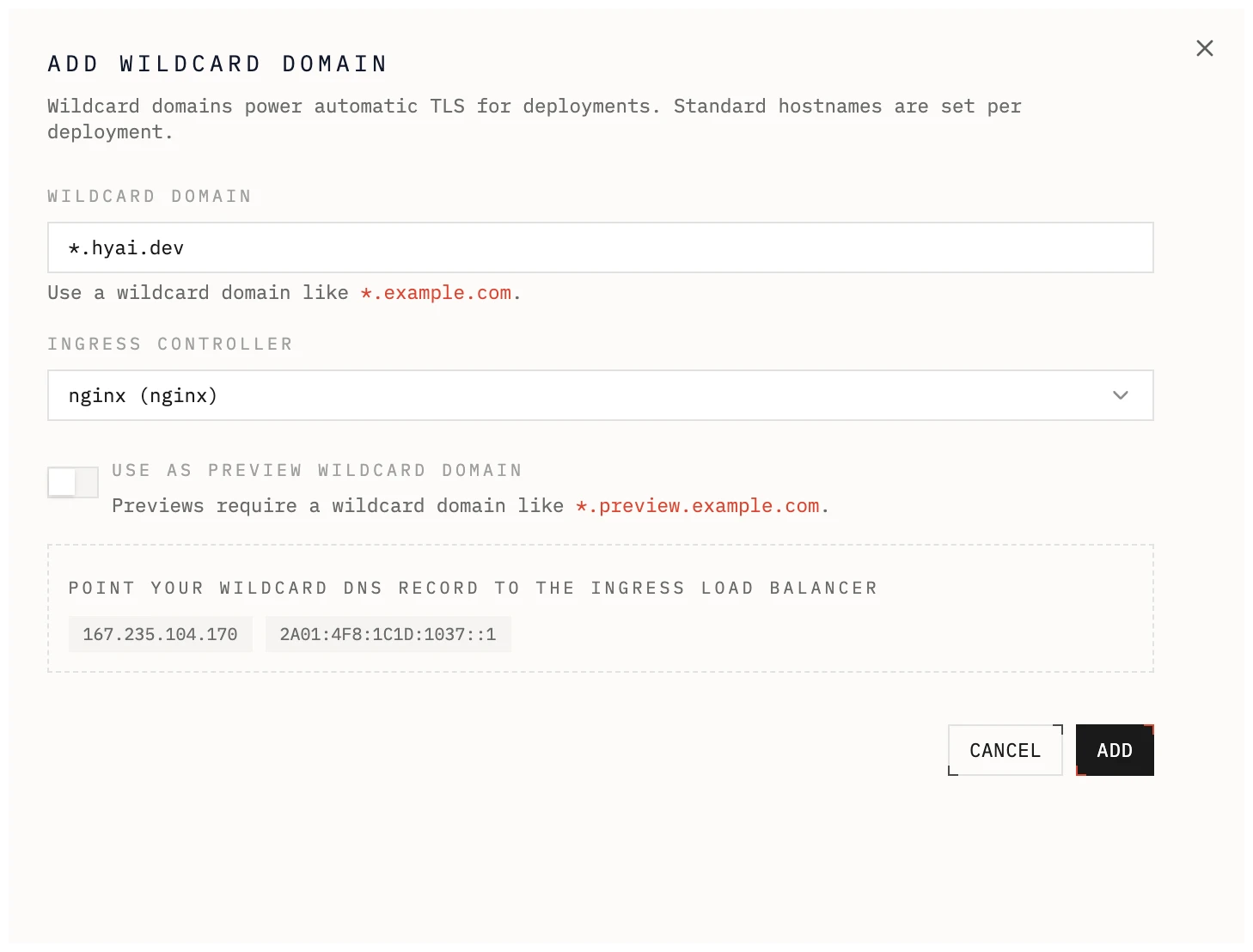
Add a wildcard domain
- Open a cluster and go to Domains.
- Add a domain like
*.example.com. - Select the ingress controller (ingress class).
- Optional: mark it as a preview domain.
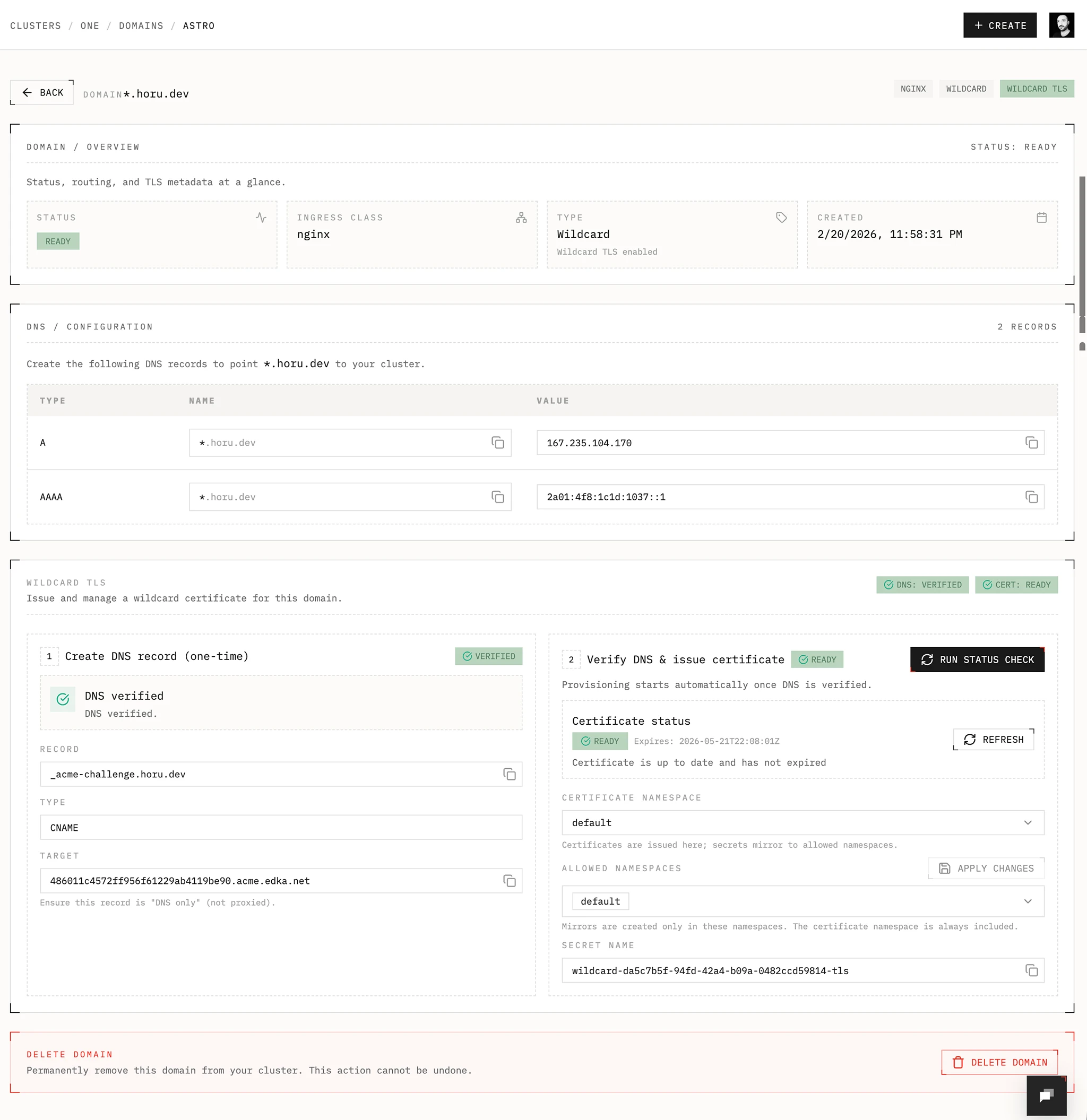
Domain verification
Step 1: Create DNS records to route the traffic to the ingress load balancer
- Use A or AAAA records to the load balancer IPs shown in the Domains view.
- Or use a CNAME to the load balancer hostname if your DNS provider supports it.
Step 2: Delegate the domain to Edka
- Create a CNAME record in your DNS provider to the Edka DNS-01 webhook.
- Name:
_acme-challenge.example.com - Type: CNAME
- Target:
<delegation-id>.acme.edka.net
Make sure the record is DNS only (not proxied). After DNS propagates, run the status check. Edka provisions the wildcard certificate with cert-manager and tracks DNS and certificate status.
Provisioning and renewal of certificates
Wildcard TLS certificates are provisioned and renewed automatically by cert-manager using the Edka DNS-01 webhook inside your cluster. You only delegate the DNS verification to Edka for improved user experience, but if you need more control, you can manually configure a DNS ClusterIssuer for cert-manager and not use the Edka DNS-01 webhook.
Requirements
- cert-manager add-on
- Edka DNS-01 webhook add-on
- Reflector add-on if you want to mirror secrets to multiple namespaces
Namespaces and secrets
- Certificate name:
wildcard-<domain-id> - Secret name:
wildcard-<domain-id>-tls - Default namespace:
defaultfor standard domains,previewfor preview domains. - Allowed namespaces control where the secret is mirrored. The certificate namespace is always included.
- If you plan to have a deployment in a namespace other than the default, for example the
productionnamespace, you need to add the namespace to the allowed namespaces. The Reflector add-on will mirror the secret to the other namespaces.
Using wildcard domains in deployments
- Set a deployment hostname like
api.example.comand enable ingress.